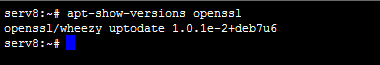
http://heartbleed.com/" onclick="window.open(this.href);return false;
and I discussed it with some freinds and it seems from the patch that it s all because of an integer roll over :
hbtype = *p++; n2s(p, payload)
and the n2s is :
#define n2s(c,s)
((s=(((unsigned int)(c[0]))<<
so if you just rollover payload value by the looks of it t gets overflow of buffer +++ whatever, so you look for the payload variable in the protocol and add 32768 to get 32768 bytes of a random pick and mix of leaked memory and voilà
anyone else studied the case of this vuln?